TIBCO BusinessConnect (BC) and its container edition (BCCE) enforce end-to-end trust through a layered security architecture designed for high-stakes B2B Document Exchange. This multi-plane approach spans transport encryption (HTTPS/SFTP), message-level encryption (S/MIME with PKI/PGP), and digital signatures. By combining channel security with payload-specific protections, TIBCO ensures data confidentiality, integrity, and non-repudiation across the entire B2B Document Exchange value chain.
Layer 1: How does TIBCO use Transport Encryption to secure the B2B Document Exchange channel?
Before a single byte of business data is moved, BusinessConnect establishes an encrypted transport channel between your system and your trading partner’s B2B gateway. This is the outermost security layer of the B2B Document Exchange, designed to prevent eavesdropping and man-in-the-middle attacks on the network connection itself.
For HTTP-based communication, BC enforces HTTPS over TLS. For file transfer, it supports SFTP (SSH File Transfer Protocol), among others. In both cases, the underlying mechanism is the same: an asymmetric algorithm negotiates a symmetric session key during the handshake, and all subsequent data flows through that encrypted channel.
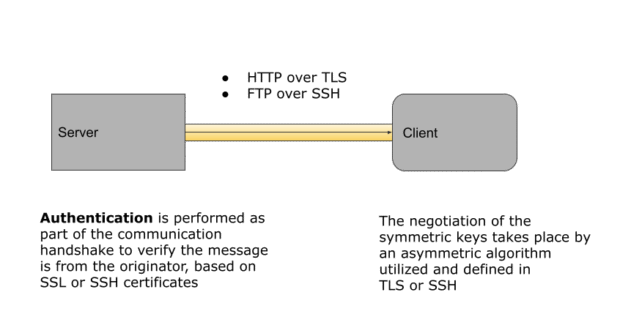
The TLS handshake is worth examining closely, because it is where certificate validation happens. When your BC instance connects outbound to a partner’s gateway, the partner presents a certificate chain — typically a leaf certificate signed by an intermediate CA, which is in turn signed by a root CA. BC validates the entire chain from leaf to root using its internal cipher platform. While BC stores a local copy of the partner’s certificate, if that copy has expired but the live certificate presented by the server passes chain validation, BC will proceed with the connection — a deliberate design choice that avoids unnecessary disruption while maintaining cryptographic integrity.
For organizations with elevated security requirements, BC also supports Mutual TLS (mTLS), where both sides present and validate certificates before the connection is established. This bidirectional authentication significantly raises the bar against impersonation attacks, at the cost of additional certificate lifecycle management overhead.
Layer 2: Why is Message-Level Encryption necessary for end-to-end B2B Document Exchange security?
Transport encryption secures the channel, but it does not protect the payload once it leaves the network layer — for example, if a message is stored, routed through an intermediary, or delivered to a system that does not enforce the same transport controls. Message-level encryption addresses this gap by encrypting the document itself, independent of the transport mechanism.
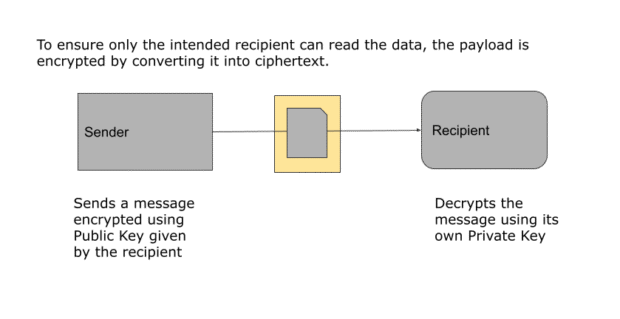
In BusinessConnect, message encryption is implemented using public/private key cryptography via either PKI (X.509 certificates) or PGP (Pretty Good Privacy), depending on what your trading partner supports. The sender encrypts the payload using the recipient’s public key. Only the holder of the corresponding private key — the intended recipient — can decrypt it. The encrypted payload is opaque to anyone else in the delivery path, including intermediaries and network infrastructure.
This model means confidentiality is enforced end-to-end, not just hop-to-hop. Even if the transport channel were compromised, an attacker would still face the full strength of the asymmetric encryption on the message itself.
Public keys in BC are represented as digital certificates — X.509 format, compliant with the PKIX standard defined in RFC 3280. These are issued by trusted Certificate Authorities such as VeriSign or GeoTrust, and BC’s certificate store holds three categories of keys: your own private keys, your partners’ public keys (certificates), and the CA root certificates used to validate the chain. Shadow certificates provide backup coverage when a certificate is approaching or has passed expiration, preventing disruption during certificate rotation.
Layer 3: How do S/MIME digital signatures ensure non-repudiation in TIBCO BusinessConnect?
The third layer addresses threat models like repudiation and tampering. Digital signatures solve this by proving that the B2B Document Exchange was initiated by a verified partner and that the content has not been altered. For industries subject to regulatory audit, this layer of the B2B Document Exchange is a compliance necessity, providing a cryptographic audit trail for every transaction.
The process works as follows: when a sender signs a document, a cryptographic digest of the message content is computed using a hashing algorithm — BC supports MD5, SHA-1, SHA-256, SHA-384, and SHA-512. That digest is then encrypted with the sender’s private key to produce the signature, which is attached to the message.
On the receiving end, the recipient uses the sender’s public key to decrypt the signature and recover the original digest. They independently compute a fresh digest of the received message content using the same algorithm. If the two digests match, two things are proven: the message was sent by the party that holds that private key (authentication), and the content has not been altered since it was signed (integrity). If they do not match, the document fails verification and should be rejected.
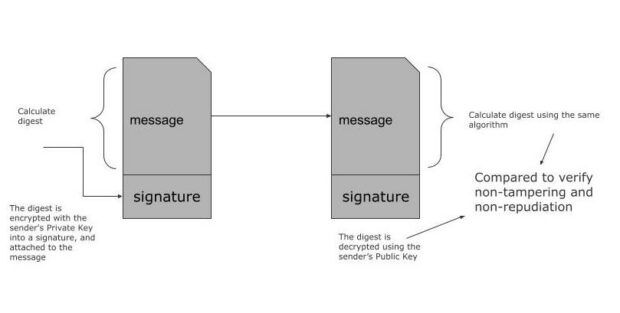
This mechanism provides non-repudiation — the sender cannot credibly deny having sent the document, because the signature could only have been produced by their private key. For industries subject to regulatory audit requirements, this is not a nice-to-have; it is a compliance necessity.
Note that the signature process is the inverse of message encryption: signing uses the sender’s private key and verifies with the sender’s public key, while encryption uses the recipient’s public key and decrypts with the recipient’s private key. Both can be applied simultaneously to the same document, giving you confidentiality and authenticity in a single pass.
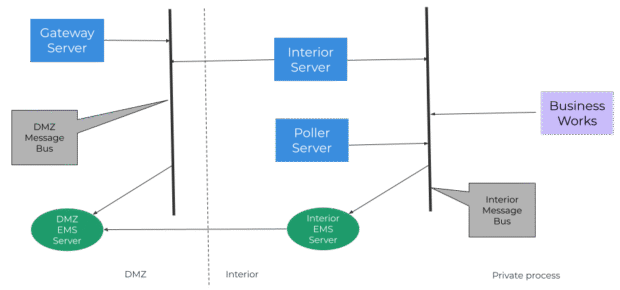
What is the recommended DMZ architecture for TIBCO BusinessConnect?
Beyond the three cryptographic layers, BCCE recommends a dual-EMS deployment (EMS = TIBCO Enterprise Message Service, one of TIBCO’s messaging platforms) within a DMZ architecture. The principle is straightforward: all inbound internet-facing connections (HTTP, FTP) terminate at a server in the DMZ. Direct connectivity to the interior application server is blocked. This separation ensures that even if a DMZ component were compromised, the interior network remains protected — a standard defense-in-depth posture that aligns with most enterprise security frameworks.
Putting It All Together
The security model in TIBCO BusinessConnect and BCCE is not a single control — it is a stack. Transport encryption protects the channel. Message encryption protects the payload end-to-end. Digital signatures prove authenticity and enforce non-repudiation. Certificate management, digest algorithm selection, and DMZ topology give your security team the controls to tune this stack to your risk profile and compliance requirements.
| Security Layer | Purpose | Key Methods/Protocols | |
| Transport | Prevent eavesdropping and man-in-the-middle attacks | HTTPS over TLS, SFTP | |
| Message Encryption | Ensure only intended recipient can read the payload | S/MIME using public-private cryptography via PKI (X.509 certificates) or PGP | |
| Digital Signature | Non-repudiation and non-tampering | Message digest is computed using SHA-1, SHA-256, SHA-384, and SHA-512 algorithms. Digest is encrypted using public-private cryptography (the reverse of message encryption). | |
For IT and InfoSec managers evaluating or currently operating a BC or BCCE deployment, understanding how these layers interact — and where each one can be configured or extended — is essential to maintaining a defensible security posture across your partner ecosystem.
Want to go deeper? Contact your account executive to schedule a technical session with our product and support engineers. Whether you are reviewing your current configuration, planning a migration to BCCE, or aligning your B2B security controls to a compliance framework, our team can walk through your specific environment and answer your questions directly.
Author:
Wens Gerdyman
Wens Gerdyman is a Principal Product Manager at TIBCO, responsible for B2B integration products. Wens has worked in product management and go-to-market roles at TIBCO and other companies. His product domain experience includes supply chain management, e-commerce, order management, and API management.