I’ve been fascinated watching the progress of CRISPR gene editing technology. In short, biologists have uncovered a mechanism that single-cell organisms use to fight against viral attacks by storing a sample of a viruses’ DNA code and then seeking and destroying it wherever it can find it. An additional mechanism can allow these cells to “cut and paste” DNA code, replacing the offending strand with something different, potentially beneficial.
CRISPR promises all kinds of innovations in gene therapy and is currently being studied as a potential cure for diseases like cancer and HIV. A few are even exploring its uses in biohacking to improve their own physiology. But some biologists have also realized that this storage mechanism can have uses beyond biology. Earlier this year, scientists encoded a GIF as DNA within bacterial cells using their CRISPR mechanism. More importantly, they were able to retrieve that data and convert it back into a digital file with no loss of information.
It’s not much of a stretch to suggest that this technology could be expanded to command the cell to somehow act on this code, effectively turning bacteria cells into microscopic biological computers. It all sounds like a far-future Phillip K. Dick story (“Do Bacteria Dream of Electric Sheep?”), but the technology is already at hand.
The ubiquity of code
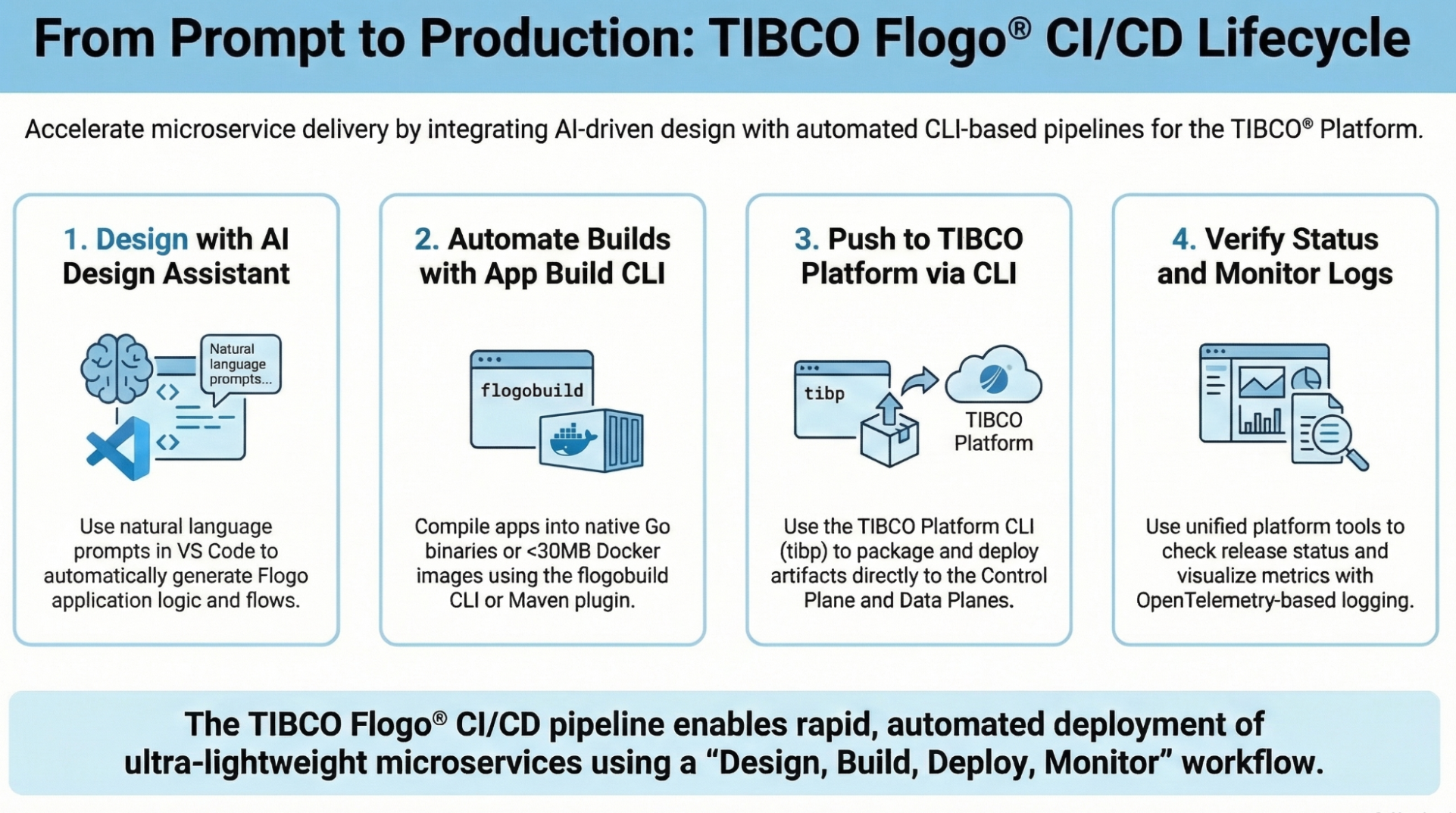
Truly decentralized apps have been just on the horizon for some time, and with the advent of microservices architecture and—most recently—“serverless” patterns that spin up a piece of code to run it only for as long as needed before putting it back into stasis, we’ve almost reached that golden horizon. The real value in the Ethereum blockchain, with its smart contracts capable of running small chunks of code across dozens of machines, had been almost totally lost amidst the hype over cryptocurrency valuations, bubbles, and instant millionaires. But the recent CryptoKitties boom proved that Ethereum is more than just a currency.
It’s more clear now than ever that the monolithic architectures of the past are rapidly being supplanted by massively distributed computational systems. The applications you write today may very well be served from one of dozens of locations—microservices running in your datacenter, Lambda services running on Amazon, or even, some day, biological computers running in a petri dish. Already, your end users don’t care where the data that drives the applications they use come from. In the near future, neither will you.
When everyone runs your code, who controls access?
The security implications of this should give you pause. When these applications are running on machines beyond your control, how can you be sure the data they’re serving is actually the right data? And how can you ensure that only the right people have access to it?
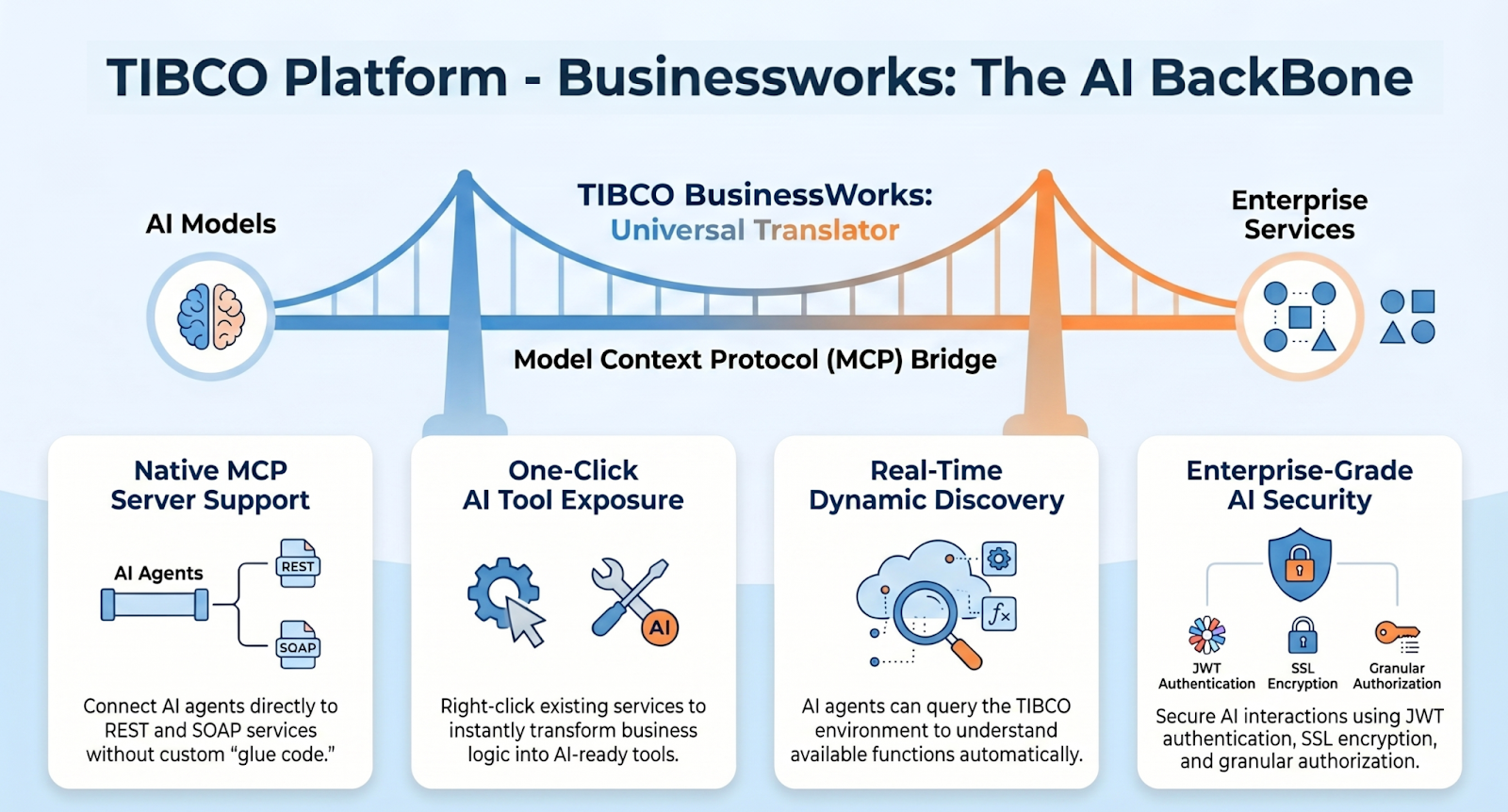
These will remain ongoing challenges as these technologies improve and progress. But tools like TIBCO’s Mashling microgateways point the way. These tools provide localized gateway control over the code they govern with the potential to configure and control them from a centralized location. As the number of services and their respective locations grow, these tools can help ensure your data is kept in the right hands and used in the way you’ve seen, no matter whose server or lab hosts it.